In a previous article, I discussed the 2020 election anomalies in Windham, New Hampshire. This article will discuss the means, motive, and opportunity for election fraud to have taken place. First, however, I would like to describe a little known but nearly identical incident that happened on the same type of AccuVote OS voting machines in the 2018 Georgia mid-term election. This small town in Georgia never got a recount or official investigation and the incident remains unexplained by state officials!
The Winterville Train Depot, Georgia Incident of 2018
According to a report by the Atlanta Journal-Constitution, the voting precinct in Winterville Train Depot, Georgia, which is located in the heavily Democratic home precinct of Georgia Governor Brian Kemp, housed seven voting machines. Democrats won every race on six of those machines, but Machine #3 delivered a Republican win in every race. This is the same anomaly that occurred in Windham except that Georgia votes were most likely flipped from Democrat to Republican candidates. To see more about this incident, go to this 2020 HBO documentary video “Kill Chain: The Cyber War on America’s Elections” and scroll to 1:07:10 (one hour and seven minutes in).
But election irregularities were not confined to this precinct. Votes for the lieutenant governor’s race, which was listed second on the voting ballot, received at least 80,000 fewer total votes than every other election in the state, including minor contests for positions such as insurance and labor commissioners. Where did the votes go? They must have been left blank, but not necessarily by the voters, as it is hard to believe that so many voters failed to select a candidate for this race. This decrease in votes took place in roughly two-thirds of the state’s electronic voting machines, but the paper absentee ballots showed no such discrepancy. It sounds to me like Democrat votes may have been flipped to blank votes for the lieutenant governor’s race, similar to the anomaly in the Windham State Representative race.
At the time of the election, Brian Kemp was Secretary of State and responsible for overseeing his own election. The voting irregularities were included among 15,500 pages of documents obtained under the Georgia Open Records Act by The Atlanta Journal-Constitution and were turned over to the U.S. House Oversight and Reform Committee. However, nothing was done. After the election, the new Georgia Secretary of State, Brad Raffensperger, refused to open an investigation. The new Governor Brian Kemp soon hired an election company lobbyist, former state Rep. Chuck Harper, to be his deputy chief of staff. Harper was a lobbyist from Election Systems & Software, the company responsible for providing technical support and repairs of the state's 27,000 Diebold voting machines and for selling the new Dominion machines to Georgia.
If there was election fraud in 2018 that benefitted Georgia Republican candidates, it is no wonder that the Republican administration would not want to investigate 2020 anomalies even if they favored Democrat candidates. They would have had too much to lose. Election fraud begets more election fraud and will result in a never-ending cycle if not broken.
Investigatory inaction or government official conflicts of interest cannot be allowed to prevail in Windham, NH. Now, let’s get to the means, motive, and opportunity to alter votes in Windham.
The Means (of altering votes)
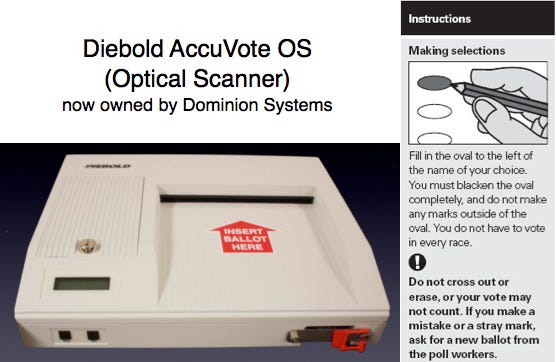
Diebold AccuVote OS (Optical Scanner) machines were first made in 1990 and have many known security vulnerabilities. The AccuVote operating system runs on Windows XP, a variant that Microsoft hasn’t supported for years and has extensive security issues. As required by state law, the machines work by optically reading paper ballots. However, votes can be easily compromised by modifying software on the election management system, the voting machines, or the memory card that gets inserted into the machine. A hand count of the paper ballots would be needed to verify any errors in the count. Go to this video excerpt from the 2006 HBO documentary “Hacking Democracy” or this longer electing hacking video and scroll to 7:00 (seven minutes in) to see a hacking test in action, where a memory card is modified and the results of paper ballot scans are changed on the official paper tape printout. This the same machine used in Windham, NH in 2020 and in Winterville Train Depot, GA in 2018.
According to a 2007 Documentation Assessment of the Diebold Voting Systems, the precinct count AV-OS memory card must be configured prior to the election with electronic ballot definitions that are created on the GEMS (election management system) computer. Then, after testing it for accuracy and functionality, the memory card is packaged and delivered to the polling place for insertion on Election Day. The memory card ballot definition stores the names of races and candidates plus the directions used for tallying and printing election results reports. At the close of the polling place, the unit can be returned to election headquarters with the memory card sealed inside or poll workers can remove the memory card and send it to be uploaded into the GEMS server. GEMS can then tabulate the results and issue the election reports. Or, the internal modem that is embedded in the AV-OS may be used to transmit vote data over the phone lines. If the modem option is used, the AV-OS apparently sends the vote data in the clear with no authentication or encryption.
In other words, the memory card is a critical part of the voting system and must be programmed for each election using the election management system. As we saw in the video above, it can cause voting machine results to be altered.
According to Ben Bynum, town clerk in Canterbury, when showing the town’s single AccuVote machine, “They cut the pins off, so you can’t put the modems back in, even if you wanted to.” So, at least the unsecure modems can’t be used.
A 2007 Source Code Review of the Diebold Voting System, conducted by the University of California, Berkeley under contract to the California Secretary of State, had numerous disturbing conclusions relevant to the AccuVote OS and the GEMS server that aggregates votes.
Vulnerability to malicious software: The Diebold software contains vulnerabilities that could allow an attacker to install malicious software on voting machines or on the election management system. Malicious software could cause votes to be recorded incorrectly or to be miscounted, possibly altering election results. It could also prevent voting machines from accepting votes, potentially causing long lines or disenfranchising voters.
Susceptibility to viruses: The Diebold system is susceptible to computer viruses that propagate from voting machine to voting machine and between voting machines and the election management system. A virus could allow an attacker who only had access to a few machines or memory cards, or possibly to only one, to spread malicious software to most, if not all, of a county’s voting machines. Thus, large-scale election fraud in the Diebold system does not necessarily require physical access to a large number of voting machines.
Vulnerability to malicious insiders: The Diebold system lacks adequate controls to ensure that county workers with access to the GEMS central election management system do not exceed their authority. Anyone with access to a county’s GEMS server could tamper with ballot definitions or election results and could also introduce malicious software into the GEMS server itself or into the county’s voting machines.
A 2005 report by Black Box Voting describes the AccuVote OS as “a house with an unlockable revolving door.” The memory cards can be read and written with any Epson RBC compatible device and contain executable (not human readable) code called AccuBasic that will be executed on the machine. The code is capable of hiding pre-loaded votes, programming conditional behavior based on hidden triggers, hiding a pre-arranged integer overflow that can reset a candidate’s votes to zero, altering audit reports, and changing the reporting of votes on printouts.
Fraction Magic: According to BlackBoxVoting.org, a study of the GEMS election management system demonstrates that a fractional vote feature is embedded in each GEMS application which can be used to invisibly alter election outcomes by pre-setting desired vote percentages to redistribute votes. GEMS fractionalizes votes in three places:
The “Summary” vote tally, which provides overall election totals for each race
The “Statement of Votes Cast”, which provides detailed results by precinct and voting method
The “undervote” count
According to programmer notes, a weighted race feature was designed which not only gives some votes more weight than others, but does so based on the voter’s identity if that identity is provided in a bar code on the ballot. Ballots are sometimes connected to voters, and weights are assigned to each voter per race, stored in an external table not visible in GEMS. So, it sounds possible to target the votes of voters based on their party affiliation, but this may not be possible in New Hampshire if the ballots do not have any voter identification on them.
Votes containing decimals are reported as whole numbers unless specifically instructed to reveal decimals (which is not the default setting). So, use of the decimalized vote feature is unlikely to be detected by auditing or canvass procedures, and can be applied across large jurisdictions in less than 60 seconds. Fractionalizing the undervote category allows reallocation of valid votes into “blank” undervotes (when a voter fails to make a choice).
However, as far as we know, there were no differences in the Windham results between the paper tape and the GEMS system results. All known discrepancies occurred between the AccuVote Optical Scan voting machines and the paper ballots. This does not mean that other jurisdictions didn’t see changes in the GEMS results, but there are currently no such allegations.
It is clear that the AccuVote OS machines used in Windham are extremely vulnerable to hacking to anyone with sufficient computer skills, motive and opportunity to access them. The paper ballots used for mail-in voting are also susceptible to anyone who is able to alter, destroy, or replace them. If a voter “undervotes” by failing to select all the candidates they are eligible to, anyone with access to the ballot can add votes with nothing more than a pen before it is submitted into the optical scanner. Ballots could also be easily destroyed and, if extra blank ballots were available, replaced with new hand-market ballots for their preferred candidate. These activities only require time with the ballots and no oversight.
The Motive (for altering votes)
The question of motive depends on who is presumed to be altering votes. There are several possible categories of malicious actors:
Candidates: Candidates running for office may want an “insurance policy” to win an election by altering votes in their own election. This is the most common form of fraud, but it is usually fairly limited in the number of votes involved, as far as we know, although consider the widespread 2018 Georgia election anomalies noted above.
Partisan Election Workers: Party activists may want to tip the balance of an election in favor of as many of their party candidates as possible or plausible, or against particular candidate who they dislike the most. Considering the widespread hatred for President Trump among Democrats and even some Republicans, it is likely that many had a strong desire to help ensure he lost the election. Partisan groups, especially if supported by a national political party or wealthy donors, would have significantly more resources.
Hackers: Leftists, anarchists, or apolitical hackers might have attempted to interfere with election integrity for political gain or for the challenge or for hire on behalf of another interested party.
Foreign Actors: Foreign nations also have an interest in seeing candidates who they dislike lose or candidates who they prefer to win. Nation states have the most significant resources and states like China, Russia, or Iran, which suffered severe economic damage from Trump administration tariffs and sanctions, almost certainly would have wanted him removed.
Election Machine Vendors: Partisan activists or foreign actors could also have influenced, through persuasion, bribery, blackmail, or other methods, the vendors who maintain the election software and systems. These vendors have the most knowledge about, and access to, their supported systems.
It is possible that a “perfect storm” of all of the above actors may have come together to create a broad attack on 2020 election results in order to oust President Trump. Others may have merely joined in to help elect themselves or their preferred candidates. Perhaps Democrats, “Never-Trump” or corrupt Republicans, anarchist/leftist activists, and foreign state actors were all involved. The situation reminds me of the Agatha Christie whodunit Murder on the Orient Express, where many different suspects all had motives for committing murder and banded together to commit the crime and protect each other. Perhaps deals were made where everyone got something from the bargain (e.g., votes for a candidate, money, election equipment contracts).
Election fraud begets election fraud, until the cycle is broken.
The Opportunity (to alter votes)
As shown above, the AccuVote OS machine results can be altered if a malicious actor has access to the election management system, the voting machines, or even just memory cards. They can also modify paper mail-in ballots if they have unrestricted, unsupervised access to fill in blank votes, destroy ballots, or even possibly add their own ballots. If they have a source of unused ballots, or a printer who can produce blank ballots, they can be filled in manually and added to the pile of genuine ballots.
So, the question is, who had access to election computers, voting machines, memory cards, or ballots? As postulated above, there could be multiple actors all attempting to modify votes for different or similar reasons. Foreign actors may have conducted cyber attacks on the election management systems and modified code that could be transmitted via memory cards to the voting machines themselves. Domestic actors may have done the same, possibly with the assistance of election machine vendors. Poll workers may have even contributed on their own with low-tech modification of paper ballots.
LHS Associates is the company that provides election services for the New Hampshire AccuVote machines. According to their website, it is “the largest provider of election services in the Northeastern US, serving more than 750 towns, cities, counties and unions throughout New England and New York. For more than 20 years, LHS marketed the highly regarded AccuVote tabulating systems. We have more than 4000 AccuVote systems installed and will continue to support the AccuVote well into the future.”
According to Windham Town Clerk Nicole Bottai, “When we tested the machines, the November election, everything was flawless,” Bottai said. “We completed our audit logs, sealed the memory cards within the machine and secured them in our vault.”
According to Canterbury Town Clerk Ben Bynum, the only way to change these machines is to insert a memory card programmed by LHS Associates in Salem, and you can’t do that unless you first cut off a metal tamper-proof seal. And if you don’t record the proper identification numbers in the proper place in the proper book with the signature of a witness, that will raise suspicions. “The secretary of state’s office comes and checks these, makes sure we’re doing them properly,” said Bynum regarding the Election Ballot Counting Device Activity Log. Speaking of those cards, how do Bynum and other clerks know they’ve been properly programmed? Clerks are required to mark up at least 50 test ballots, including some incorrect votes (e.g., two names marked when only one seat is open), and then run them through each voting machine.
In a 2008 interview about Diebold machines, the reliability of their memory cards was discussed. They apparently have a high failure rate and are often replaced, even on Election Day, contrary to protocol.
“The vendor, LHS Associates, arrives on the scene and they're going to fix this problem. Most of the time when I find those kinds of problems and I check with officials, the officials don't know what's happened.… And they're surprised. And they also tend to say, 'That wasn't how it was supposed to be done.' … So we really have to start looking into the failure rate of the memory cards, the security of the machines and, of course, when you have any problem on Election Day, that means you have a much greater vulnerability to fraud. And so I've seen a lot of articles about New Hampshire, and the initial articles basically pooh-poohed the idea that the machines could be a problem or have been hacked. Because of the paper ballot and because they are the optical scanners. This is a mistake. These machines are just as vulnerable to fraud, tampering and also just really technical failure as any other Diebold machine.”
The CEO of LHS Associates, Jeff Silvestro, attended the Board of Selectmen election incident meetings in Windham, NH. His presentation was allegedly full of misrepresentations. If it is true that LHS Associates programs the memory cards and starts the chain of custody for these election artifacts, the company must be considered as a possible prime suspect, an accomplice, or at least a possible victim of third party hacking of their network without their knowledge.
Other possible suspects could include poll workers at each precinct, but involving too many people would be an obvious problem for anyone who does not want to get caught. When committing illegal acts, it is better to keep the number of people involved or “in the know” as small as possible and limit their exposure to suspicion.
Where to Start an Investigation
If I were to pursue an investigation of voting machine tampering, it would begin with LHS Associates and the AccuVote memory cards. If I were to pursue an investigation of paper ballot tampering, it would begin with workers who were part of the chain of custody of those ballots, especially if they had access to ballots from multiple jurisdictions or the opportunity to access ballots without oversight prior to Election Day after envelopes had been opened. Let’s hope that the planned forensic audit of the Windham results is thorough. All paper ballots need to be checked, including those with “blank” undervotes and overvotes. Particular attention should be paid to the type of ink used to manually mark votes to ensure that it is consistent for each vote on the ballot. The type of paper and printer ink should also be examined to ensure it is a genuine ballot.
Biden flipped the counties of Hillsborough, Rockingham, Carroll, and Sullivan into the Democratic column for Joe Biden. Hillsborough and Rockingham are the two most populous counties. In the 2012 presidential election, Time had listed Hillsborough as one of five critical counties affecting the outcome in the swing state of New Hampshire. Manchester is the state's largest city, followed by Nashua, and are both in Hillsborough County, while Windham is in Rockingham County. Eighty percent of New Hampshire's votes are counted by computers, while the other 20 percent are counted manually (mostly in smaller or more rural areas).
I should also note that there was concern in the 2008 Democrat primary that candidate Hillary Clinton received a higher percentage of the vote, especially in Manchester and Nashua, from voting machines, while Barak Obama received a higher percentage in hand-counted areas. When a hand recount was conducted, there was a significant discrepancy in the totals for all of the top Democrat candidates. These errors were attributed to human error from two different clerks in two different districts who made similar errors recording the totals from the machine counts.
If I were to expand the investigation outside of Windham to pursue a state-wide investigation of the 2020 election results, I would start in Manchester and Nashua.
If fraud is detected in New Hampshire elections, I would not stop once the most obvious suspect has been identified. It is highly likely that there were multiple participants in the attack on our election systems in 2020 and earlier. When it became obvious years ago that our election systems were not secure, it was only a matter of time before more and more actors decided to exploit these weaknesses. It will only get worse if we do not stop it now.









We need an attorney here in NH and they are all corrupt or scared to take the case. Any ideas?
It’s apparent from some work Bill Brown did that scatter/blank ballots could be used to prop up Sheehan. Take a look at this www.election-research.com.